Mobile Application Security’s Best Practices for Developers
Top 10 Mobile App Security Best Practices for Developers
The most convenient way to scroll through any business platform is the use of its application. Even if it is not an e-commerce application, any gaming, personal, or banking application is prowl to intruders.
Mobile application security has become a necessity these days. Your single mistake and your entire personal and professional data can be at stake. A single breach is enough to cause you a loss of millions of dollars and on top of that, the customer trust you lose is irreparable.
With this kind of monetary as well as reputational loss, the developers need to be on their toes and prioritize the need to secure their mobile apps from the very moment they begin to write the first line of code. Here are a few Mobile application security’s tips that as a developer you should look up to while developing the mobile app,
1. Write a secure code
From the very first day you begin with code writing, you need to find ways to be a step ahead of the hackers. Bugs and vulnerabilities in code are what an attacker looks for. They try to get hold of the public copy of the code, apply reverse engineering and do tampering with it. Research shows that around 11.6 million mobiles are prone to attack due to the presence of malicious codes.
You need to obfuscate and minify your code to make it difficult to break through and reverse engineer. Repeated testing and bug fixing are necessary and there is a need to generate an agile code that can be updated at the user end post a breach.
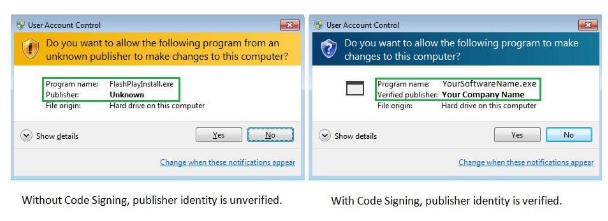
2. Use of Code signing certificate
Code signing certificates offers a digital signature that a developer uses to sign software or a code to ensure the user that the code has not been tampered with. This reassurance gives a user an impression that the code comes from a genuine publisher and the mobile app is safe to use and download.
It is essential to sign a code using a code signing certificate, especially when you are distributing your application via a third-party vendor. There are several low cost or cheap code signing certificates available in the market that can be availed to experience great security. Few of them are Sectigo Code Signing certificate, Comodo Code Signing certificate, DigiCert Code Signing certificate, etc.
3. Choose third-party libraries carefully
It has become a necessity to use third-party libraries to ease down the coding process. However, before we use a third-party library, we need to be extra cautious and test it extensively for vulnerabilities.
Recent have seen that many libraries were prone to vulnerabilities and security flaws that resulted in attacks on mobile apps. Controlled repositories must be used and policy controls must be executed to safeguard the apps from intruders.
4. Penetration testing
A penetration test is necessary to avoid any risk and vulnerability that a mobile app can be prone to. In penetration testing, the code is tested against general security scenarios to check for vulnerabilities. Absolute loopholes are detected in such attempts and penetration testing helps to eliminate these potential threats to cause cyberattacks.
5. Encrypt all data
Encryption is the foremost step to securing your data. Every mobile app surely has a flow of data from inside out and vice-versa. Security of such data is crucial to safeguard the users as well as other organizational data and information. Here the plain text is scrambled and only the one who has access to the private key can decrypt the data. The power of encryption is such that high-end organizations like the FBI and NSA are asking for permission to access iPhone and WhatsApp messages.
Also Read: Top 25 Programming Languages for Mobile Application Development
6. Use the best cryptography tools and techniques
Key management is crucial to safeguard the mobile app from vulnerabilities. Some of the most popular algorithms like SHA1 and MD5 have failed to live up to the growing security threats. Use vital algorithms like AES with 512-bit encryption, 256-bit encryption along with SHA-256 for hashing. Such standards are best to keep your keys safe from hackers. Also, make sure you never store your keys locally.
7. Use the least privileged principle
Your code depends on the specifics of your apps, so never ask for unnecessary permissions from your users. Use the least privilege approach, and ask for permission for only necessary things that are necessary to run the app. This means that do not ask to access the contacts if you do not need them to run the application.
8. High-level authentication
Some of the well-known and vital security breaches have occurred because of poor authentication policies. You need to abide by strong authentication measures to secure your mobile apps.
Design your app such that it only takes in alphanumeric passwords that need renewal every three months. In addition, the prominent multi-factor authentication policy must be incorporated that uses static passwords and dynamic OTP to login into a device. They can further use biometric scans to ensure utmost security.
9. Test repeatedly and get regular updates
Penetration testing, emulators and threat modelling are renowned methods that need to be incorporated to have a regular check on vulnerabilities. Thus, repeated testing makes the code bug free. Also, generate regular updates and issue patches whenever necessary to fix the desired issues.
10. Minimize storage of sensitive data
It is highly recommended that as a developer you do not store sensitive data into the device’s local memory, as it is prone to be of high risk. If you are left with no other option than to store data, do it in encryption containers or key chains to keep them safe. Also, deploy an auto-delete option, which deletes the data after a certain fixed period.
Also Read: Best Mobile App Development Companies In India 2023
Final takeaway
The last few years have seen some of the most iconic breaches and have made everyone look upon the cybersecurity of their mobile apps. From organizations to customers, everyone wants to invest their money and time in an app, which secure. Mobile application security has become a priority of mobile app developers. The above-curated list of security practices will help you get on your toes and let those potential customers know that you are trustworthy.